Examples & Guides
Practical implementation patterns, antifraud playbooks, and production-ready integration recipes.
Use this section as a working library: architecture ideas, rollout checklists, and clear examples
for login, signup, checkout, and anti-abuse scenarios.

Tired of false positives crippling your cross-border e-commerce checkout flow? This guide dives into location anomaly suppression thresholds, turning raw GeoIP data into actionable intelligence for fraud prevention. We'll explore practical implementation strategies and help you build a system that minimizes risk and maximizes conversions. Because getting it wrong is costing you real money.Let's drill down into the practical aspects of building a dynamic threshold engine. This isn't just about setting numbers; it's about creating a system that learns and adapts, from basic to robust ML driven approaches.
Read article

Learn how to implement robust geo-based fraud loss forecasting models to comply with regulations, minimize financial risks, and improve the accuracy of fraud detection. This practical guide helps you build a resilient system by establishing clear geo validation rules, implementing thorough logging requirements, ensuring audit readiness, and proactively managing geo-feature drift within your machine learning models. Enhance your geo-validation techniques through behavioral analysis, effectively handle temporary location changes, optimize data storage, and manage imprecise location data for a stronger, more reliable system across your organization's enterprise SSO and geo-aware access architecture.
Read article
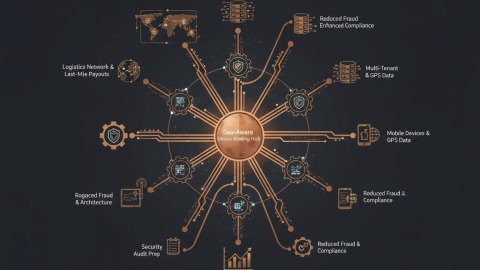
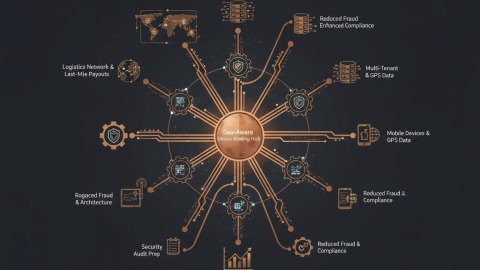
Prepare for your next security audit with this deep dive into geo-aware device binding strategies. Learn how to implement robust geo-fencing and contextual device authorization to mitigate fraud in logistics and payment systems. Secure your multi-tenant architecture with precise geo-filtering. Actionable checklists and deployment examples included.
Read article

Subscription abuse bleeds revenue, but false positives kill legitimate expansion. Here's how to architect a B2B monitoring system that balances risk and revenue in a global context, focusing on practical geo-based detection and fraud triage A/B testing.
Read article

Learn how to model risk transitions between countries and Autonomous System Numbers (ASNs) to enhance fraud detection in cross-border insurance operations. This guide provides practical steps to improve your authentication and claims validation processes, balancing security with growth.
Read article
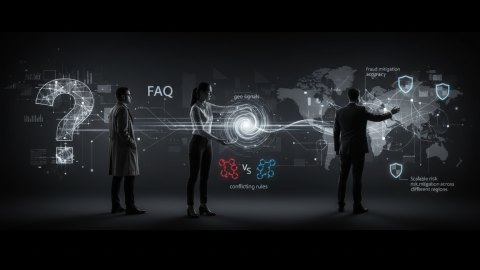
A comprehensive FAQ on implementing geo-informed fraud governance models. Learn how to calibrate geo signals, resolve conflicting rules, and improve fraud mitigation accuracy across different regions to protect your business.
Read article

Region-based botnet fingerprinting is critical for accurate risk assessment, especially in industries with stringent data residency requirements. This article analyzes distinct approaches to regional botnet detection, highlighting the trade-offs between precision, performance, and compliance. We'll explore practical implementation strategies and a geo data quality audit checklist to improve alignment between product and fraud teams.
Read article
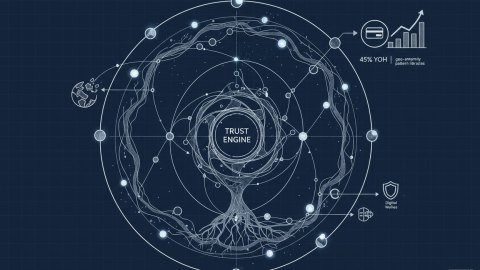
In the fintech realm, especially within card issuing and wallet ecosystems, detecting and mitigating fraudulent activities hinges on robust geo-anomaly detection. This article delves into architecting pattern libraries that empower fraud teams to proactively identify and address geographically improbable transactions, enhancing compliance and safeguarding revenue. We'll cover practical strategies, from data modeling to feature engineering, providing concrete examples to bolster your fraud defenses.
Read article

Discover how to architect a geo-informed trust system that balances global growth with robust security. Explore risk taxonomies, system design, API contracts, and edge cases to build a scalable and secure architecture.
Read article

Learn how to combine geolocation data with device fingerprinting for stronger fraud prevention in fintech systems. This article explores practical implementation techniques to enhance security and reduce risk. Includes code examples and architecture design considerations.
Read article