Examples & Guides
Practical implementation patterns, antifraud playbooks, and production-ready integration recipes.
Use this section as a working library: architecture ideas, rollout checklists, and clear examples
for login, signup, checkout, and anti-abuse scenarios.

Discover how to architect a geo-informed trust system that balances global growth with robust security. Explore risk taxonomies, system design, API contracts, and edge cases to build a scalable and secure architecture.
Read article

Learn how to combine geolocation data with device fingerprinting for stronger fraud prevention in fintech systems. This article explores practical implementation techniques to enhance security and reduce risk. Includes code examples and architecture design considerations.
Read article

Future-proof your SaaS by architecting a robust cross-border subscription abuse detection system. Learn about decision frameworks, risk appetite thresholds, and escalation logic to protect your revenue stream and build trust with your customers.
Read article

Understand how to leverage geographical data from web and mobile sessions to improve customer engagement, optimize marketing spend, and enhance security. This article provides a clear architectural approach and practical implementation guidelines for C-level executives and technical architects.
Read article

Implement robust risk scoring for roaming mobile IP addresses in fintech to mitigate fraud and ensure compliance. This article details a practical approach to manage the unique challenges of mobile roaming in financial transactions.
Read article

Explore advanced techniques for geo-aware device binding, including multi-source location data, adaptive geo-fencing, and device profiling. Learn how to architect scalable systems and continuously monitor for optimal compliance and security.
Read article

Learn how to proactively identify and mitigate location-based risks in your system architecture using a structured audit framework. Understand the threat model, abuse cases, and implementation steps to prevent costly breaches like the infamous 'North Korean ATM heist'.
Read article

Explore the data-backed approach to enhancing passwordless authentication with geo-based risk scoring. This guide provides a threat model, implementation details, and mitigation strategies to secure B2B systems against location-related fraud.
Read article
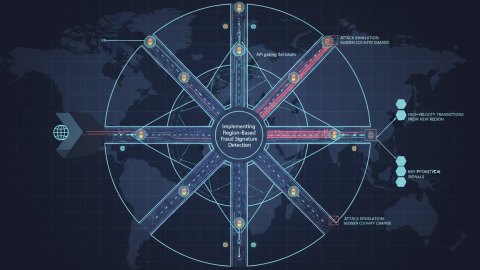
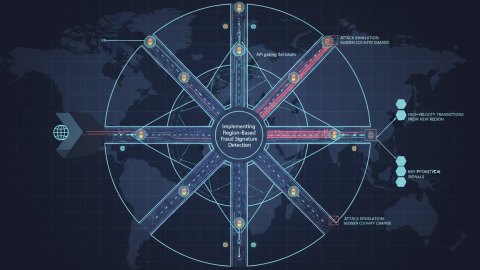
This field report details the practical implementation of region-based fraud signature detection, focusing on architectural decisions, implementation specifics, and lessons learned. We explore attack simulations, key detection signals, and effective countermeasures, emphasizing a hands-on approach.
Read article

Implementing effective location risk decision audit logging is crucial for B2B security and compliance. This guide provides a checklist-driven approach to designing, implementing, and monitoring your location-based risk assessment processes, alongside advanced configuration and optimization practices.
Read article