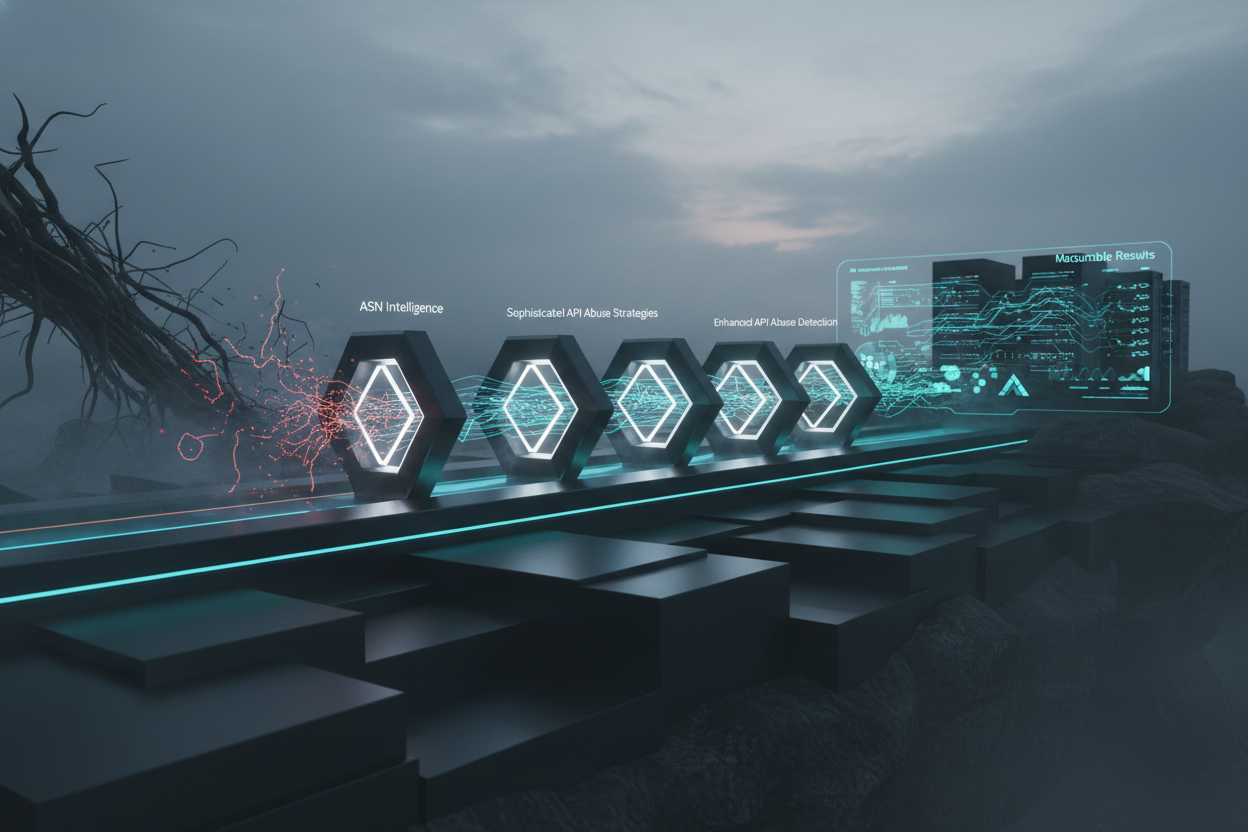
Leveraging ASN Intelligence for Enhanced API Abuse Detection: A Case Study
Introduction: The Growing Threat of API Abuse
APIs (Application Programming Interfaces) are the backbone of modern software architecture, enabling seamless communication and data exchange between applications. However, their increasing popularity makes them prime targets for abuse and malicious attacks. Traditional security measures often fall short in identifying and mitigating sophisticated API abuse strategies. This is where Autonomous System Number (ASN) intelligence becomes a crucial asset. Let's dive into how we've seen it used.
This architecture note presents a case study illustrating the effective use of ASN intelligence to detect and prevent API abuse. We'll focus on a practical, real-world scenario, highlighting the challenges, solutions, and tangible benefits achieved by incorporating ASN data into API security protocols. This isn't theoretical – it's based on helping clients every day.
Checklist: Is ASN Intelligence Right for Your API Security?
Before diving deep, let's quickly assess if ASN intelligence can benefit your organization. Consider these questions:
- Do you observe suspicious API traffic originating from unexpected geographic regions?
- Are you experiencing brute-force attacks or credential stuffing attempts on your API endpoints?
- Do you need to differentiate between legitimate user behavior and automated bot activity?
- Are you concerned about API scraping or data theft?
- Do you lack precise details about the source of incoming API traffic?
If you answered yes to one or more of these questions, then ASN intelligence can be a valuable addition to your API security toolkit. It's about having richer context for your decision-making.
Environment Checks: Preparing for ASN-Based API Defense
Before implementing ASN-based API security, perform these crucial environment checks:
1. Understand Your API Traffic Patterns
Analyze historical API traffic data to establish a baseline of typical user behavior. Identify common geographic locations, request frequencies, and calling patterns.
2. Evaluate Your Existing Security Infrastructure
Assess the capabilities of your current API gateway, WAF (Web Application Firewall), and intrusion detection systems. Determine how ASN intelligence can be integrated into these existing components. Often, clients only address the API gateway itself, and later regret waiting to evaluate other security layers.
3. Choose an ASN Data Provider
Select a reliable ASN data provider. A good partner will have accurate, up-to-date ASN information. Ensure the provider offers the data points you need, such as the ASN owner, registration date, and network type. Pay close attention to update frequencies.
4. Secure Data Handling
Consider data regulations in your target markets. Design your integration to be properly compliant with GDPR, CCPA, and other privacy regulations. This is primarily about policy and implementation.
Risk Rule Setup: Crafting ASN-Driven Security Policies
The core of leveraging ASN intelligence lies in creating risk rules based on ASN attributes. Here's a breakdown of common rules and how to configure them:
1. Blocking Known Malicious ASNs
Create a blacklist of ASNs associated with known malicious actors, such as botnet operators or providers of anonymization services. This is a simple but effective way to filter out unwanted traffic.
Example: Block all traffic originating from ASNs known to host Tor exit nodes. This can prevent attackers from masking their true location.
2. Geolocation-Based Restrictions
Implement rules that restrict API access based on the geographic location of the ASN. This is useful if your API is intended for use only within specific regions.
Example: Block traffic from ASNs located in countries with a history of API abuse or fraud. This can help reduce the risk of unwanted attacks.
3. Anomaly Detection Based on ASN Usage
Identify unusual API usage patterns based on ASN. For instance, a sudden surge in requests from a previously inactive ASN could indicate a bot attack.
Example: Flag any ASN that exceeds a predefined request threshold within a given time period. This can help identify potential denial-of-service (DoS) attacks.
4. Reputation Scoring Based on ASN History
Assign reputation scores to ASNs based on their historical behavior. ASNs with a history of malicious activity should receive lower scores and be subject to stricter scrutiny.
Example: Reduce access privileges for ASNs with a history of spamming or other abusive behavior. This can help mitigate the impact of compromised accounts.
5. Validating New ASN Registrations
Be wary of traffic originating from newly registered ASNs, as these may be used for testing attack infrastructure. Implement rules that require additional validation steps for these ASNs.
Example: Require CAPTCHA verification for users connecting through ASNs registered within the last 30 days. This can help prevent automated bot activity.
Integration Steps: Putting ASN Intelligence into Action
Integrating ASN intelligence into your API security architecture involves these steps:
1. API Gateway Integration
Integrate ASN lookup functionality directly into your API gateway. The gateway should query the ASN data provider for each incoming request.
2. Data Enrichment
Enrich API request data with ASN information, such as the ASN owner, geographic location, and reputation score. This enriched data can be used for more informed decision-making.
3. Policy Enforcement
Configure your API gateway or WAF to enforce the risk rules you defined earlier. This may involve blocking requests, throttling traffic, or requiring additional authentication steps.
4. Real-time Threat Response
Implement real-time threat response mechanisms that automatically react to suspicious activity based on ASN intelligence. This can help quickly mitigate attacks and prevent data breaches.
Case Study Example: A SaaS company noticed a spike in API requests from a handful of ASNs located in Eastern Europe. After investigation, they discovered that these ASNs were associated with a botnet attempting to scrape user data. By blocking traffic from these ASNs, the company was able to immediately mitigate the attack and prevent further data theft.
For a working example of the architecture for this, see: API Rate Limiting Architecture.
Monitoring Controls: Measuring Success and Adapting to Change
Continuous monitoring is essential to ensure the effectiveness of your ASN-based API security. Implement these monitoring controls:
1. Track ASN-Based Blocking Rates
Monitor the number of API requests blocked based on ASN rules. This provides insights into the prevalence of malicious activity and the effectiveness of your blocking policies.
2. Analyze False Positive Rates
Carefully analyze false positive rates (legitimate requests incorrectly blocked). Fine-tune your risk rules to minimize false positives while maintaining effective security.
3. Monitor ASN Reputation Scores
Track changes in ASN reputation scores over time. A sudden drop in reputation score could indicate a compromised ASN or the emergence of new malicious activity.
4. Review Security Logs
Regularly review security logs to identify suspicious patterns and anomalies. This can help uncover new attack vectors and refine your ASN-based security policies.
Case Study: Reducing API Scraping by 70% with ASN Intelligence
One of our clients, a data analytics firm, suffered heavily from API scraping, resulting in increased infrastructure costs and potential data breaches. Standard rate limiting was ineffective due to attackers rotating IPs within large ASNs. By implementing ASN-based throttling, specifically targeting ASNs known for hosting scraping bots, they observed a 70% reduction in scraping attempts within the first month. This dramatically decreased server load and improved data security.
This client now uses ASN reputation scores in combination with behavioral analysis to tailor their security responses, such as presenting CAPTCHAs or requiring multi-factor authentication for suspicious ASNs.
Conclusion: Embracing ASN Intelligence for a Secure API Future
ASN intelligence is a powerful tool for enhancing API security and mitigating the risk of abuse. By understanding ASN attributes, creating targeted risk rules, and continuously monitoring API traffic, businesses can significantly improve their security posture and protect their valuable data. Just as defense has many layers, so too should your API security.
In conclusion, consider the practical benefits illustrated in this case study and proactively integrate ASN intelligence into your API security roadmap. For additional ideas, see: API Design Best Practices. Also, consider reviewing: API Security Checklist.
Try It In Your Product
Ready to apply this pattern? Start with a free API test, issue your key, and proceed to docs.
Next step
Run a quick API test, issue your key, and integrate from docs.