Scalable API Abuse Detection with ASN Intelligence
Blue Team Guide to API Abuse Detection with ASN Intelligence
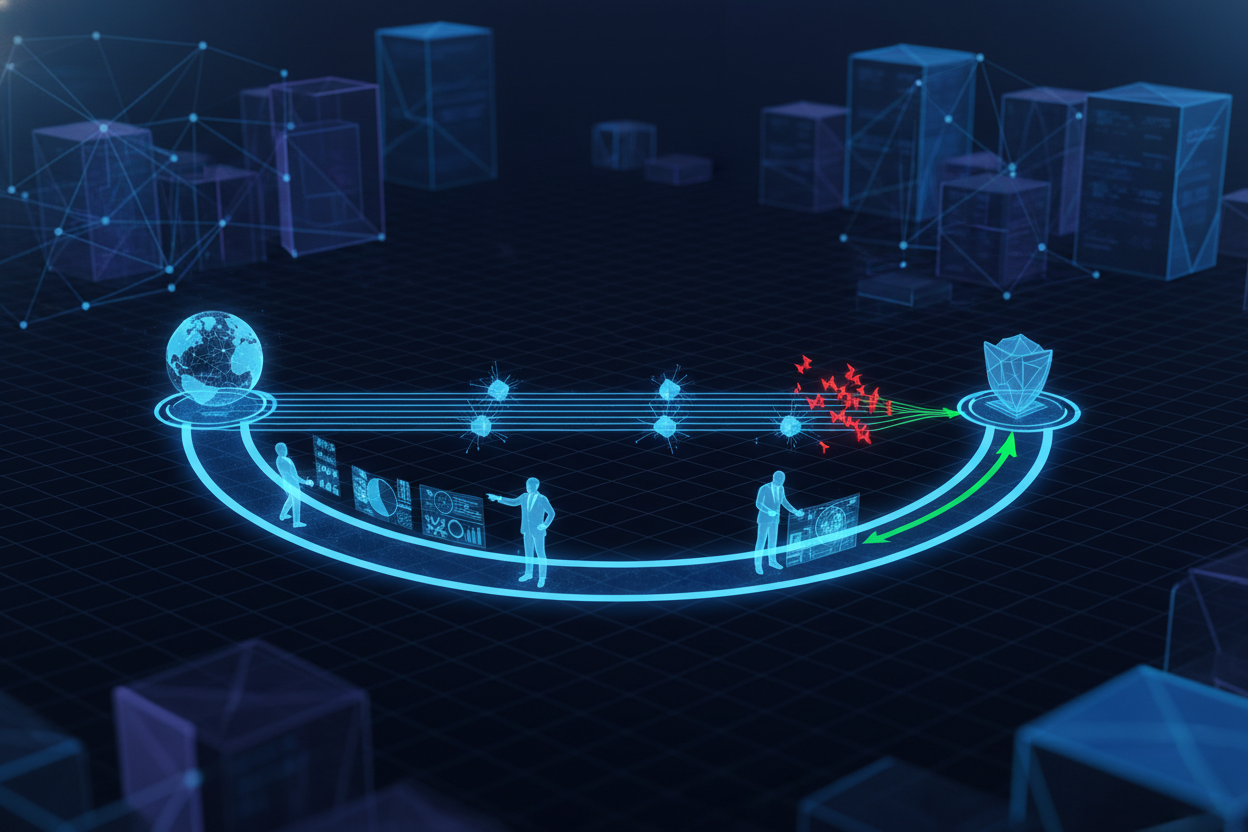
Protecting APIs from abuse requires a scalable approach that goes beyond simple IP address blocking. Autonomous System Numbers (ASNs) provide valuable context about the origin and network characteristics of incoming traffic. By incorporating ASN intelligence into your API abuse detection strategy, you can identify and mitigate threats more effectively, ensuring your infrastructure remains resilient under load. This guide outlines a practical, scalable framework for leveraging ASN data in your security operations.
Understanding the Role of ASN in API Security
An ASN is a unique identifier assigned to an autonomous system, which is a network or a group of networks controlled by a single administrative entity. ASN information can reveal the organization responsible for originating traffic, the type of network (e.g., residential, business, hosting provider), and potentially malicious activity patterns associated with specific ASNs. This data is invaluable for enhancing API security, particularly regarding scalability and identifying coordinated attacks coming from infrastructure providers frequently abused by bad actors.
Alert Triage: Prioritizing Incidents with ASN Context
The volume of security alerts can be overwhelming. ASN data can significantly improve alert triage by providing contextual information that helps security teams prioritize incidents effectively. Focus on signals that point towards scalable abuse patterns rather than one-off occurrences.
Checklist for ASN-Based Alert Triage
- Identify the ASN: Determine the ASN associated with the source IP address of the alert.
- Assess ASN Reputation: Check if the ASN is known for hosting malicious activities (e.g., botnets, proxy services).
- Analyze Traffic Patterns: Investigate if the ASN exhibits unusual traffic patterns or sudden surges in API requests.
- Correlate with Other Signals: Combine ASN data with other indicators (e.g., request rate, user agent consistency) to assess the severity of the alert.
- Prioritize High-Risk ASNs: Focus on alerts originating from ASNs with a poor reputation or suspicious activity patterns.
Investigation Workflow: Uncovering the Root Cause
Once an alert is prioritized, a thorough investigation is crucial to understand the nature and scope of the abuse. ASN intelligence plays a central role in identifying the source of the attack, its potential scale, and its impact on your API infrastructure.
Steps for Investigating API Abuse with ASN Data
- ASN Profiling: Examine the ASN's registration details, peering relationships, and routing policies.
- Traffic Analysis: Analyze the traffic originating from the ASN, looking for patterns such as high request rates, unusual API endpoints, or suspicious payloads.
- Historical Data: Review historical data associated with the ASN to determine if it has been involved in previous attacks.
- Reputation Data: Check the ASN's reputation with third-party threat intelligence feeds and community blacklists.
- Attribution: Attempt to attribute the abuse to a specific organization or actor based on the ASN's characteristics and associated intelligence.
Geo Pivots: Visualizing ASN-Based Attacks on a Map
Integrating geographical data with ASN intelligence adds another layer of context to API abuse investigations. Mapping ASN locations can reveal patterns in attack origins, helping you pinpoint regions or networks that are disproportionately contributing to malicious activity. Consider this especially when scaling globally.
Using Geo Pivots for ASN Intelligence
- Visualize Attack Origins: Plot the geographical locations of ASNs associated with API abuse incidents on a map.
- Identify Hotspots: Look for clusters of malicious activity originating from specific regions or countries.
- Analyze Routing Paths: Examine the routing paths of traffic originating from suspicious ASNs to understand how it reaches your API.
- Consider Data Privacy: Handle geographical data responsibly, adhering to privacy regulations and minimizing the collection of sensitive information.
- Scale your mapping solution: Ensure your visualization tools can handle large volumes of ASN and geographical data without performance bottlenecks.
Automation Scripts: Streamlining Responses at Scale
Manual investigation of API abuse is time-consuming and inefficient. Automation is key to scaling your security operations and responding to threats in real-time. Develop automation scripts that leverage ASN intelligence to identify and mitigate malicious activity programmatically.
Example Automation Script (Python):
import requests
def check_asn_reputation(ip_address):
# Replace with your ASN intelligence API endpoint
url = f"https://api.example.com/asn_info?ip={ip_address}"
response = requests.get(url)
data = response.json()
asn = data.get('asn')
reputation_score = data.get('reputation_score')
if reputation_score > 0.8:
print(f"High risk ASN: {asn}")
# Implement blocking logic here
else:
print(f"ASN: {asn}, Reputation Score: {reputation_score}")
# Example usage
ip_address = "1.2.3.4"
check_asn_reputation(ip_address)
Prevention: Blocking Malicious ASNs
Based on the insights gained from alert triage, investigation, and geo pivots, take proactive steps to prevent API abuse by blocking known malicious ASNs. This strategy should be implemented carefully to avoid blocking legitimate traffic.
Anti-Patterns to Avoid
- Overly Aggressive Blocking: Blocking entire ASNs without careful consideration can disrupt legitimate traffic.
- Static Blacklists: Relying solely on static blacklists can lead to false positives and miss emerging threats.
- Lack of Monitoring: Failing to monitor the impact of ASN blocking can result in unintended consequences and operational issues.
Best Practices for ASN-Based Prevention
- Implement Dynamic Blocking: Use real-time threat intelligence and behavioral analysis to dynamically block malicious ASNs.
- Monitor Traffic Impact: Continuously monitor the impact of ASN blocking on legitimate traffic and adjust your policies accordingly.
- Use Rate Limiting: Implement rate limiting policies to prevent abuse from specific ASNs without completely blocking them.
- Consider Whitelisting: Whitelist known good ASNs to ensure that legitimate traffic is not affected by blocking policies.
- Automate Updates: Automate the process of updating ASN blacklists and whitelists based on the latest threat intelligence.
Leveraging ASN intelligence is a powerful way to enhance your API abuse detection and prevention capabilities, enabling you to maintain a secure and scalable API infrastructure. By understanding how to triage alerts, investigate incidents, and implement automated prevention strategies, you can effectively mitigate the risks associated with API abuse and protect your valuable assets. For practical examples of rate limiting strategies, see our article on rate limiting strategies.
For a deeper dive into API security best practices, see our article on API security best practices. And learn how to build continuous security integration in CI/CD pipelines.
Next step
Run a quick API test, issue your key, and integrate from docs.