Implementing Webhook Fraud Signal Pipelines with GeoIP Enrichment
Introduction
Fraud prevention systems require rapid, reliable data flows to detect and mitigate threats in real time. One common bottleneck lies in processing webhooks for fraud, as webhooks often pass unfiltered data. By enriching these webhooks with GeoIP signals, you can significantly improve accuracy and reduce false positives. This implementation guide will walk you through building a webhook fraud signal pipeline with GeoIP enrichment, maximizing efficiency and effectiveness.
If you're new to GeoIP-based fraud detection, learning how enrichment works is key. Simply put, GeoIP enrichment adds geolocation data and additional risk indicators to a webhook's payload based on the sender's IP address. This enriched data enables informed decisions about blocking, trusting, or escalating traffic.
Quick Start: Defining the Webhook Fraud Signal Flow
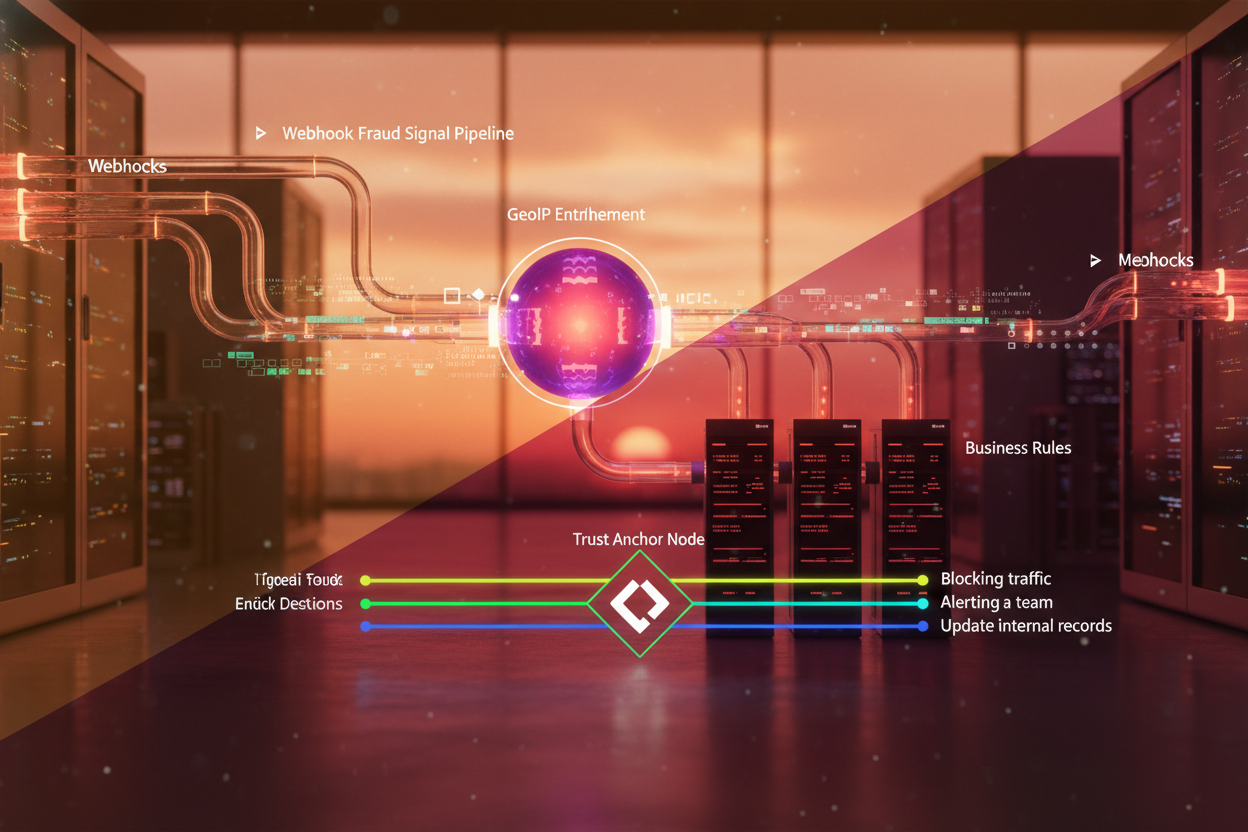
To get started, let's clearly define the data flow for our webhook fraud signal pipeline:
- A webhook is triggered by an external event (e.g., a login attempt, transaction, or API request).
- The webhook payload is forwarded to your backend or middleware.
- GeoIP enrichment is applied to the IP address within the payload to append geolocation and risk signals.
- Business rules utilize the enriched data to score or classify the event as fraudulent or legitimate.
- Actions are triggered based on the classification, such as blocking traffic, alerting a team, or updating internal records.
This quick start will focus on processing the IP address and augmenting the webhook payload with GeoIP data using the GeoIP.space API.
Prerequisites
- Access to the GeoIP.space API and API key.
- A backend system capable of processing and forwarding webhooks.
- Basic knowledge of JSON data structures and HTTP methods.
Basic Python Example
Here’s a minimal code path to integrate GeoIP enrichment into a Python webhook processor:
import requests
def process_webhook(webhook_payload):
ip = webhook_payload.get("ip_address")
if not ip:
raise ValueError("IP address missing in webhook payload")
geoip_response = requests.get(
f"https://api.geoip.space/v1/enrich",
headers={"Authorization": "Bearer YOUR_API_KEY"},
params={"ip": ip}
)
if geoip_response.status_code == 200:
enriched_data = geoip_response.json()
webhook_payload["geoip"] = enriched_data
return webhook_payload
else:
raise Exception(f"GeoIP API request failed: {geoip_response.status_code}")This example assumes your webhook payload includes an ip_address key. Replace YOUR_API_KEY with your GeoIP.space API key.
Minimal Code Path: Extending for Event Classification
Adding Fraud Scoring Rules
Once the payload is enriched, you should implement simple rules to flag suspicious activity. For instance, you might compare the user's country or ASN to trusted lists or check for anomalies like frequent location changes. Here’s how you can expand the example:
def classify_event(webhook_payload):
geoip_data = webhook_payload.get("geoip")
if not geoip_data:
raise ValueError("GeoIP data missing from payload")
country = geoip_data["location"]["country"]
risk_score = geoip_data["risk"]["score"]
if country not in ["US", "CA"]:
return "flagged"
elif risk_score > 70:
return "high_risk"
else:
return "legitimate"Integrate this classification logic into your webhook handlers to automate simple decisions.
Production Hardening
While the above example works for proof-of-concept (POC) development, production systems require several enhancements for scalability and reliability:
1. Retry Logic
Because external APIs can occasionally fail, implement retry logic with exponential backoff to minimize downtime and errors. Here’s an example:
import time
def fetch_geoip_with_retries(ip, retries=3):
for attempt in range(retries):
try:
response = requests.get(
f"https://api.geoip.space/v1/enrich",
headers={"Authorization": "Bearer YOUR_API_KEY"},
params={"ip": ip}
)
if response.status_code == 200:
return response.json()
else:
time.sleep(2 ** attempt) # Exponential backoff
except requests.exceptions.RequestException:
time.sleep(2 ** attempt)
continue
raise Exception("GeoIP enrichment failed after retries")2. Data Sanitization
Ensure webhook payloads are sanitized to prevent injection attacks. For example, validate and encode all user-input values.
3. Secure API Credentials
Store your API keys securely, such as in environment variables or a secrets management service. Avoid hardcoding keys in your source code.
Monitoring and Logging
Real-time fraud signal pipelines benefit from robust monitoring and logging to troubleshoot failures and track trends.
- Request Logging: Log GeoIP API requests and the returned data for debugging.
- Fraud Trends: Track flagged events by type, location, or score to adjust thresholds and refine rules dynamically.
- Alerting: Set up alerts for anomalies, like a sudden spike in high-risk scores.
Implementing comprehensive monitoring ensures the system's performance and effectiveness are maintained over time.
Next Steps
By following this guide, you've set up a basic webhook fraud signal pipeline with GeoIP enrichment and added foundational elements for classification. To further improve your system, consider the following:
- Read Optimizing Fraud Scoring Systems: Reducing False Positives with a GeoIP-Centric Architecture for advanced methods to refine fraud scoring.
- Explore Coupon Abuse Controls by Location Risk Segments: Architecture & Implementation to extend GeoIP enrichment to areas like promotional abuse detection.
- Sign up for the GeoIP.space dashboard to start analyzing real-world data and managing your API integrations more effectively.
Conclusion
Webhook fraud signal pipelines enriched with GeoIP data allow your system to make smarter, real-time decisions. By implementing the outlined steps, you’ve built a foundation ready for production hardening, monitoring, and further optimization. Begin exploring the full capabilities of GeoIP.space API to empower your antifraud systems today.
To implement these patterns in production, create an account and test the API on real traffic.
Related reads
Advanced Event Classification: Custom Rules and Strategies
Once the basic fraud scoring rules are in place, you can implement advanced classification strategies to improve accuracy and flexibility. This involves a combination of real-time checks, behavioral analysis, and contextual awareness. Below are some practical techniques you can adopt:
- Time of Access Validation: Add rules to flag activity occurring at unusual times based on the user's historical behavior or the timezone from GeoIP enrichment. For example, transactions from regions with significant time differences to the user's profile might indicate fraudulent activity.
- ASN Trust Levels: Evaluate the Autonomous System Number (ASN) in the GeoIP data. Certain ASNs, such as those tied to data centers or VPN providers, can be flagged as higher risk depending on your risk appetite.
- Location Velocity Checks: Calculate the time difference between events and the geographical distance using the latitude and longitude provided by GeoIP. If a user appears to "travel" impossibly fast between events, it is a strong fraud indicator.
- IP Reputation Scoring: Integrate GeoIP risk factors, such as IP reputation scores, into your classification logic. Traffic originating from IPs with known suspicious activity should be flagged as high-risk and possibly require further review.
- Multi-Factor Rules: Combine multiple signals—such as location, ASN, risk score, and device information—to assign a composite fraud risk score that dynamically adjusts based on weighted parameters customized to your business needs.
By creating composite scoring mechanisms, you can better distinguish legitimate users from attackers and reduce false positives, especially in environments with high traffic volumes.
Batch Processing for High Volume Workflows
In scenarios where webhook traffic is high, processing each event synchronously can become a performance bottleneck. Instead, consider implementing batch processing for GeoIP enrichment and classification. Here's how:
- Buffer incoming webhook events in a message queue or processing pipeline.
- Group events by IP address and request enrichment data from the GeoIP.space API in batches. This reduces redundancy and conserves API usage limits.
- Distribute enrichment data back to individual payloads, applying fraud scoring rules to each item.
- Trigger downstream actions asynchronously, such as flagging accounts or updating records.
Here’s an example of pseudo-code for batch processing:
def batch_process_webhooks(webhook_payloads):
unique_ips = set(payload.get('ip_address') for payload in webhook_payloads if payload.get('ip_address'))
# Request GeoIP enrichment for all unique IPs
geoip_data = {}
for ip in unique_ips:
geoip_response = requests.get(
f"https://api.geoip.space/v1/enrich",
headers={"Authorization": "Bearer YOUR_API_KEY"},
params={"ip": ip}
)
if geoip_response.status_code == 200:
geoip_data[ip] = geoip_response.json()
# Enrich each webhook payload
for payload in webhook_payloads:
ip = payload.get('ip_address')
if ip in geoip_data:
payload['geoip'] = geoip_data[ip]
return webhook_payloadsBatch processing prevents service disruptions and optimizes resource utilization. However, ensure buffer sizes and queue limits are tuned to your system capacity to avoid latency issues.
Audit Trails and Event Correlation
Fraud detection often benefits from detailed audit logs that capture enriched payload data, rule evaluations, and subsequent actions. Implement structured logging that includes:
- Event Metadata: Include timestamps, webhook IDs, and enriched GeoIP fields for each event.
- Rule Execution Logs: Record which rules were triggered and the corresponding outcomes (e.g., "Rule X: High Risk Based on ASN").
- Actions Taken: Detail actions performed, such as blocked IP addresses, flagged accounts, or escalation notifications.
For example, you might log a successful event as follows:
{
"timestamp": "2023-10-05T12:00:00Z",
"event_id": "abc123",
"ip": "192.168.1.1",
"geoip": {
"location": {"country": "US", "city": "New York"},
"risk": {"score": 25}
},
"rule_results": [
{"rule": "Country Trusted", "result": true},
{"rule": "Risk Score Check", "result": false}
],
"action": "approved"
}Audit logs not only aid in compliance and troubleshooting but also enable deeper event correlation for further insights. For instance, patterns visible across timestamps or geolocations can help refine fraud prevention strategies.
Scaling Your Fraud Pipeline
As your traffic grows, the infrastructure supporting your fraud detection pipeline must scale effectively. Consider the following components for scalability:
- Load Balancing: Distribute webhook events across multiple backend workers to enhance throughput and reduce processing latency.
- Horizontal Scaling: Deploy additional instances of your webhook processors to handle increased traffic without degrading performance.
- Rate Limiting: Use rate-limiting cues in the GeoIP.space API to stay within API quotas while prioritizing high-risk or priority events.
- Database Optimization: Optimize database queries for log storage and rule evaluations. Consider caching frequently accessed GeoIP data to minimize repetitive API calls.
Your system’s scalability is directly tied to its ability to handle rapid spikes in fraudulent activity without delays or missed threats.
Ensuring Resiliency with Fault Tolerance
System failures can undermine the reliability of fraud pipelines. Designing with fault tolerance ensures uninterrupted operations:
- Fallback Mechanisms: If GeoIP enrichment fails, implement fallback logic using cached data or approximate risk values to maintain basic functionality.
- Redundancy: Employ redundant queues and API gateway endpoints to avoid a single point of failure.
- Graceful Degradation: Define a prioritized workflow for critical events like financial transactions to proceed even during partial service outages.
Fault-tolerant architectures safeguard both the pipeline's robustness and your users’ trust during high-stake operations.
Next step
Run a quick API test, issue your key, and integrate from docs.