Implementing Region-Based fraud signature detection: a field report
Region-Based Fraud Signature Detection: A Field Report
Fraud detection is a constantly evolving arms race. A crucial component of a robust fraud prevention system involves analyzing the geographic origin of transactions and user activities. This report outlines our experience implementing a region-based fraud signature detection system, providing practical insights for architects and developers. We will describe a concrete implementation focused on identifying anomalous patterns related to the geographic origin of requests.
Red Team Perspective
Before building a detection system, it's vital to understand how it might be bypassed. From a red team perspective, attackers may attempt to:
- IP Spoofing: Using proxy servers or VPNs to mask their true location.
- Compromised Accounts: Gaining control of legitimate user accounts and performing fraudulent actions from the account's established region, then suddenly shifting regions.
- Regional Proxy Networks: Utilizing botnets distributed across different geographic regions to mimic normal user behavior.
Understanding these attack vectors is crucial for designing an effective region-based fraud detection system. For example, if an attacker can spoof an IP address from a trusted region (e.g., using a residential IP proxy), the system must rely on additional signals to accurately identify fraud. We must aim to defeat these attack vectors.
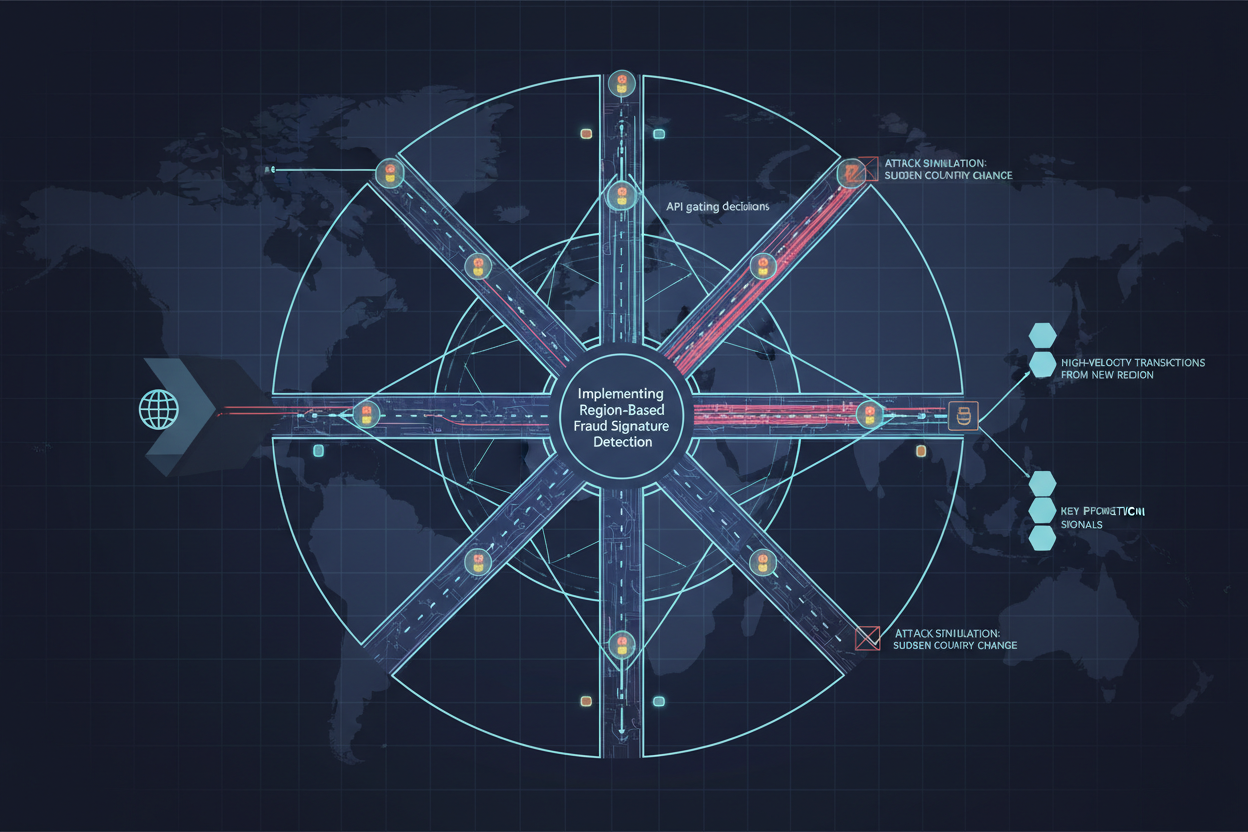
Attack Simulation
To test the effectiveness of our fraud detection mechanisms, we simulated different attack scenarios:
- Sudden Country Change: A user typically accessing the service from the US suddenly originates requests from Russia.
- High-Velocity Transactions from New Region: An account that usually performs one transaction per day starts executing hundreds of transactions from a new country within a short period.
- IP Address Anomaly: A user logs in using an IP address that has a high fraud score.
These simulations allowed us to identify weaknesses in our initial detection logic and fine-tune our system's sensitivity. We found that a simple country-based comparison was insufficient, leading us to incorporate more sophisticated methods.
Detection Signals
The key to effective region-based fraud detection is identifying reliable signals. We focused on these factors:
- GeoIP Data: Utilizing GeoIP databases to determine the location (country, region, city) of the user's IP address. Consider the accuracy levels, and regularly update the GeoIP database for freshness.
- Transaction History: Tracking the typical geographic locations from which a user or account normally transacts.
- Velocity Checks: Monitoring the number of transactions originating from a new or unusual region within a specific timeframe.
- Device Fingerprinting: Using device fingerprinting techniques to identify if the device's location matches the advertised IP location.
- Billing Address/Shipping Address Mismatch: Comparing the billing address and shipping address with the IP address location. Significant discrepancies trigger flags.
Combining these signals provides a more comprehensive view and reduces the likelihood of false positives. For example, a sudden change in country for a single transaction might be a false alarm, but a high-velocity series of transactions from a new region coupled with a device fingerprint mismatch would be a strong indicator of fraud.
Countermeasures
Based on the identified signals and attack simulations, we implemented the following countermeasures:
- Real-time Risk Scoring: Assigned a risk score based on the combined weight of the detection signals. Higher scores trigger more aggressive countermeasures.
- Transaction Blocking: Automatically blocking transactions originating from high-risk regions or exhibiting suspicious region-related patterns.
- Account Freezing: Temporarily freezing accounts with suspicious activity pending manual review.
- Two-Factor Authentication (2FA) Trigger: Requiring 2FA for logins from unfamiliar regions.
- Step-Up Authentication: Asking challenge questions or requiring additional verification for suspicious transactions.
The choice of countermeasures depends on the severity of the risk and the potential impact on legitimate users. We implemented a tiered approach, with less disruptive measures (e.g., 2FA) applied to lower-risk scenarios and more aggressive measures (e.g., transaction blocking) reserved for high-risk cases.
Code References
Implementing region-based detection requires integrating with a GeoIP service and building custom logic to analyze patterns. Below is a simplified example (pseudocode) of how you might implement basic region-based validation:
function analyzeTransaction(transaction, userProfile) {
ipAddress = transaction.ipAddress;
geoData = getGeoIPData(ipAddress);
country = geoData.country;
if (userProfile.trustedCountries.contains(country)) {
return RISK_LOW;
}
if (transaction.amount > MAX_TRANSACTION_AMOUNT && country !== userProfile.defaultCountry) {
return RISK_HIGH; // High risk transaction from unknown country
}
// More complex scoring logic based on velocity, device fingerprint, etc.
return RISK_MEDIUM;
}
This script outlines a way to use a GeoIP lookup along with historical transaction data with a simple risk engine. See more complex examples on incorporating multiple data sources and rule sets in these advanced examples: Fraud Detection with Multiple Signals.
Be aware that performance is essential for systems like these, and can inform your decisions on whether to use an in-memory cache, such as Redis, to reduce GeoIP lookup latency.
Lessons Learned
Our implementation of region-based fraud signature detection yielded several key lessons:
- GeoIP Accuracy Varies: GeoIP data is not always 100% accurate. Build in tolerance and rely on other signals for confirmation. Some commercial GeoIP Solutions may provide higher quality geolocation data, which can affect latency and precision.
- User Behavior Changes: Legitimate users may travel or relocate, leading to false positives. Provide clear communication and easy methods for users to verify their identity.
- Constant Monitoring is Essential: Fraudsters are constantly evolving their techniques. Continuously monitor the system's performance and adapt the detection logic accordingly. Iterate this process periodically.
Region-based fraud detection is a valuable layer of defense against fraudulent activities. By understanding attack vectors, leveraging relevant detection signals, and implementing appropriate countermeasures, you can significantly mitigate the risk of fraud. Remember to focus on continuous monitoring and improvement to stay ahead of evolving threats. You can also explore implementing Real-Time Transaction Risk Scoring for a more complete solution. Consider Data Normalization for a system more maintainable in the long run.
Try It In Your Product
Ready to apply this pattern? Start with a free API test, issue your key, and proceed to docs.
Next step
Run a quick API test, issue your key, and integrate from docs.