Advanced Multi-Account Farm Detection Using IP Graphs and user_id: Implementation Blueprint
Introduction
Multi-account farms present a significant risk to businesses offering incentives, gaming platforms, subscription-based services, and any platform vulnerable to fraudulent exploitation. These farms operate multiple accounts simultaneously to exploit discounts, abuse referral programs, or manipulate algorithms. Effective detection requires a combination of unique user identifiers (user_id) and IP graph analysis, leveraging GeoIP data to expose hidden relationships between accounts and their network behaviors.
This article dives into the technical architecture, patterns, and implementation strategies to detect multi-account farms. We’ll also explore why combining user_id and IP graph heuristics is crucial for success and provide actionable examples to guide your deployment using the GeoIP.space API.
FAQ: Key Questions on Multi-Account Farm Detection
1. What is a multi-account farm?
A multi-account farm refers to a coordinated operation where an individual or group creates and operates numerous accounts using overlapping credentials, devices, or IP addresses. These accounts are often exploited for financial gains, rewards, or to manipulate metrics on platforms.
2. Why are IP graphs important for detection?
An IP graph visualizes relationships between user activity, shared devices, and network connections. By modeling these relationships, anomalies such as high IP sharing, overlapping session patterns, and device-level correlations can be detected efficiently.
3. How does user_id strengthen detection?
While IP graphs focus on network behaviors, user_id (a persistent identifier representing individual users) provides longitudinal data to track behavior at the account level. Combining the two ensures both behavioral patterns and inter-account connectivity are analyzed comprehensively.
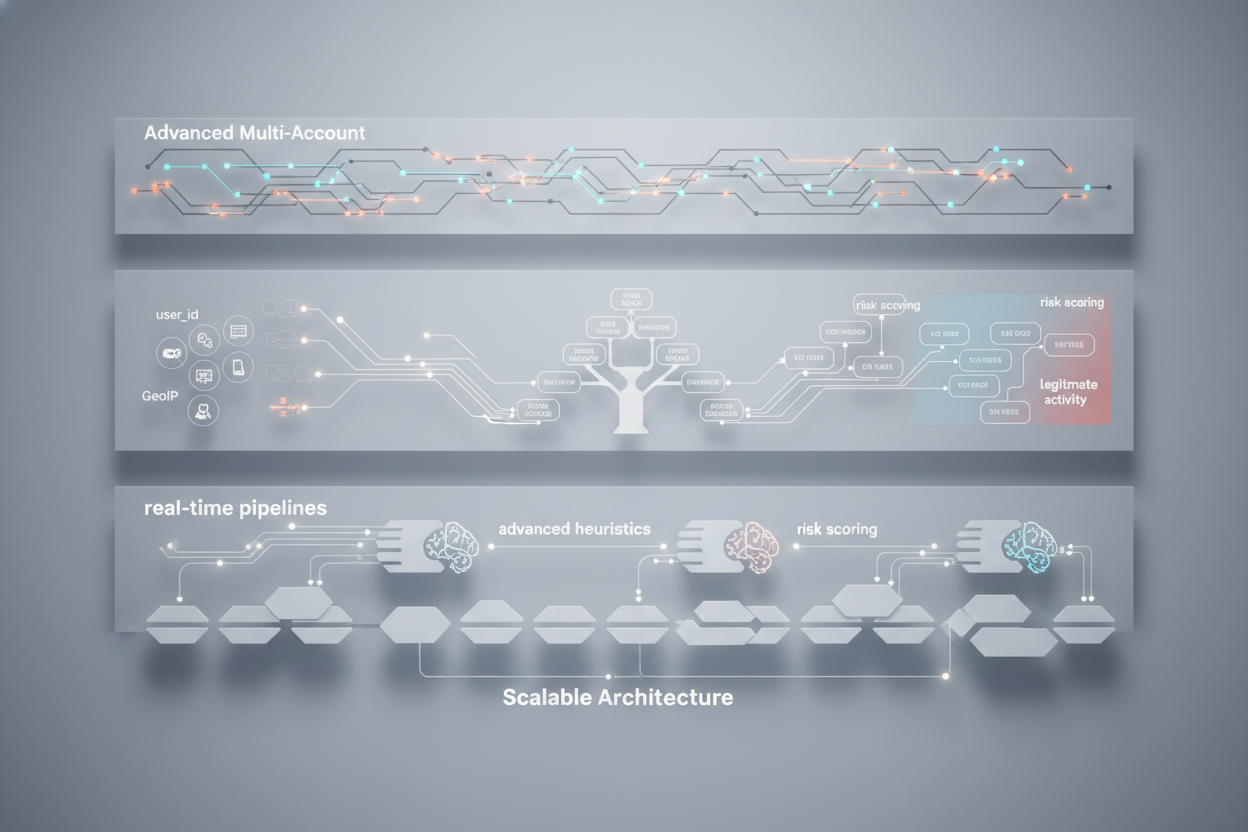
Defining the Architecture for Multi-Account Detection
1. System Overview
The system for detecting multi-account farms involves three key components:
- Data Collection: Capture IP addresses, device information, and session details for all users in real-time or near-real-time.
- Data Modeling: Build user_id linkage graphs and IP connectivity graphs, aggregating behavior by session, location, and device identifier.
- Anomaly Detection: Use heuristics or machine learning models to flag suspicious activity, such as overlapping sessions, sustained fraudulent behavior, or unrealistic usage patterns.
2. Role of GeoIP Signals
GeoIP signals enrich the architecture by introducing geographic contextualization. By linking user activity to country, region, ASN (Autonomous System Number), and IP risk scores, GeoIP data exposes anomalies such as unexpected account clustering from a residential IP or multiple regions logging into the same set of accounts.
3. Designing the IP Graph
The IP graph forms the foundation for detecting multi-account relationships. Create the graph as follows:
- Nodes: Represent user accounts (via user_id) and IP addresses.
- Edges: Define connections between accounts and IPs (e.g., User A logged in from IP 1.2.3.4).
- Edge Weighting: Introduce metrics such as session overlap, geographic risk, or frequency of use to add context to relationships.
This structure allows for algorithmic application of community detection techniques (e.g., clustering), enabling quick insights into farms operating within shared IP groupings.
Common Patterns in Multi-Account Farm Detection
1. IP Sharing Patterns
Fraud clusters often rely on the same IP address across multiple user_id values. Look for:
- High density of accounts originating from a single residential or mobile IP.
- Frequent switching between distinct accounts under the same IP in short time windows.
2. Geo Discrepancies
Use GeoIP signals to flag anomalies, such as:
- Improbable location transitions (e.g., logging in from two continents within minutes).
- Accounts operating exclusively from high-risk regions or proxies.
3. Time-Based Behavioral Anomalies
Time is a critical parameter in multi-account detection:
- Look for burst activity where multiple accounts log in from the same IP over short intervals.
- Analyze the time-of-day patterns; farms often operate during unconventional hours driven by automated scripts.
Implementation Steps: Detecting Multi-Account Farms
Step 1: Collecting and Preprocessing Data
Utilize the GeoIP.space API to capture key metrics:
{"ip": "8.8.8.8", "asn": "15169", "country": "US", "region": "CA"}Ensure all collected data is stored in a real-time database such as Redis or PostgreSQL, structured with user_id, timestamps, IPs, and GeoIP metadata.
Step 2: IP Graph Construction
Develop a graph generator function to link users and IPs for visualization and analysis:
def generate_ip_graph(data):
graph = {}
for session in data:
user_id = session['user_id']
ip = session['ip']
graph.setdefault(ip, []).append(user_id)
return graphThe above function builds a dictionary where keys are IPs and values are lists of user_ids connected to those IPs.
Step 3: Suspicious Cluster Detection
With the graph created, apply clustering algorithms or heuristic evaluations such as detecting high edge weights or suspiciously dense subgraphs.
Step 4: Adding GeoIP Risk Layers
Enrich clusters with GeoIP.space risk scores. For example:
if geoip_data['risk_score'] > threshold:
mark_ip_as_suspicious()Case Study: Real-World Application
Businesses relying on referral programs reported a 37% decrease in fraudulent accounts after deploying IP graph analysis. GeoIP-based tools flagged proxy-heavy regions and correlated this data with IP-to-user mappings for multilayered anomaly detection.
Explore similar techniques in our article: Proactive Chargeback Prevention Using GeoIP Signals: An Implementation Guide.
Checklist for Effective Detection
- Ensure correct user_id generation and storage strategies.
- Implement real-time IP graph modeling for dynamic risk assessment.
- Leverage GeoIP data to enrich entity relationships with location-based insights.
- Analyze overlapping session patterns, high-risk IPs, and rapid account switching behaviors.
Anti-Patterns to Avoid
- Over-reliance on static IP risk lists: Modern farms use dynamic proxies to evade static detection systems.
- Ignoring behavioral patterns: Focusing solely on IP addresses without incorporating user behavior misses significant context.
Conclusion
Combining user_id linkage with IP graph heuristics creates a solid framework for identifying multi-account farms. The integration of GeoIP signals adds an additional layer of precision, mitigating risk while preserving a smooth user experience.
Integrate GeoIP.centralized antifraud into your workflows today to streamline detection. Sign up now via GeoIP.space Dashboard and start strengthening your defenses.
Related reads
Step 5: Deploying Real-Time Detection Pipelines
With the earlier steps implemented, the final piece involves creating real-time pipelines to identify and act on multi-account farms without significant user delays. Follow these steps:
- Stream Data: Utilize tools like Apache Kafka or AWS Kinesis to stream login activity and GeoIP API outputs directly into your processing layer.
- Graph Incremental Updates: Instead of rebuilding the entire IP graph on every new session, incrementally update nodes and edges to reflect recent activity dynamically.
- Automatic Alerting: Integrate event triggers for suspicious subgraph clusters or GeoIP risk thresholds. For instance:
event_emitter.trigger('alert', {cluster_id: 'abc123', risk_score: 9.0});. - Block and Flag: Auto-flag user_ids linked to suspicious clusters and challenge them with CAPTCHAs or two-factor authentication (2FA). Alternatively, restrict further actions such as withdrawals or high-value transactions until verification is completed.
Step 6: Monitoring and Optimization
After deployment, continuous monitoring is crucial to ensure the effectiveness and adaptability of your system over time. Here are some strategies:
- False Positive Reviews: Regularly analyze flagged clusters to ensure legitimate users are not penalized. Refine risk thresholds based on observed false positives.
- Feedback Loops: Use identified fraudulent patterns to train machine learning models, enhancing future detection capabilities. For example, apply unsupervised learning methods to uncover previously unknown relationships.
- System Audits: Conduct periodic reviews of user_id and IP graph integrity to identify edge cases or overlooked anomalies.
Advanced Heuristics for Enhanced Detection
If your system encounters advanced fraud tactics that bypass basic detections, consider introducing these advanced heuristics:
- IP Chaining: Monitor sequences of IPs used by a single user_id to spot patterns indicative of botnets or rotating proxy networks.
- Edge Decay: Implement time-decay models for edge weights, reducing the influence of stale data while focusing on recent activity.
- Account Age Factors: Combine IP and GeoIP insights with metadata such as account creation date and initial activity patterns to identify "fresh" farm accounts.
Scaling for High Traffic Volumes
Large-scale applications require the ability to scale detection systems to handle millions of user events and IP relationships. Key considerations for scaling include:
- Database Management: Use partitioned databases or data lakes optimized for graph-based querying. For instance, Neo4j can handle highly interconnected datasets effectively.
- Parallel Processing: Break down the IP graph into smaller, independent subgraphs that can be processed in parallel using distributed computation frameworks.
- Edge Optimization: Only store significant edges that surpass thresholds for risk or activity frequency, reducing overall graph complexity.
Example Query for Anomaly Detection
Here’s a query blueprint to detect clusters flagged as high risk:
SELECT user_id, ip, COUNT(*) AS sessions, MAX(risk_score) AS max_risk
FROM user_sessions
WHERE risk_score > 7.5 OR geo_discrepancy = true
GROUP BY user_id, ip
HAVING COUNT(*) > 3;This query focuses on user_ids and IPs exhibiting significant activity patterns tied to high GeoIP risk signals. Adjust thresholds to align with your project’s sensitivity requirements.
Visualization and Reporting
To make informed decisions, integrate advanced visualization tools that allow fraud analysts to interpret your data effectively. Include features such as:
- Node Graph Visualizations: Display user_id and IP connections using color-coded nodes to represent activity levels and risk scores.
- Geo Heatmaps: Map GeoIP activity distributions to reveal unusual clusters in residential or proxy-heavy regions.
- Drill-Down Reports: Enable detailed analysis for selected user_ids, detailing login histories, associated metadata, and flagged behaviors.
Effective visualization uncovers patterns that algorithms might miss or helps validate automated conclusions during audits.
Key Metrics to Track
Monitoring the right metrics can ensure your detection system’s efficiency and continuous improvement. Focus on:
- Detection Accuracy: Percentage of confirmed farms flagged by the system versus false positives.
- Response Time: Average time between identifying a suspicious cluster and taking mitigation action.
- Coverage: Percentage of total traffic analyzed by the IP graph and GeoIP layers.
Track these metrics in a dedicated dashboard to allow engineers and risk teams to make data-driven adjustments as needed.
Business Impact of Multi-Account Detection
The benefits of implementing a robust multi-account detection system go beyond reducing fraud. Direct and indirect advantages include:
- Revenue Protection: Stop abuse of promos, rewards, and other financial incentives lost to fraudulent farms.
- User Trust: Preserve the satisfaction of genuine users by eliminating bad actors early.
- Operational Efficiency: Reduce reliance on manual reviews or repetitive ticket handling by trust and safety teams.
Investing in advanced systems like IP graphs combined with GeoIP.space significantly enhances business scalability while mitigating reputational risk.
Next step
Run a quick API test, issue your key, and integrate from docs.