Geo-Aware device binding: a security audit prep guide for logistics
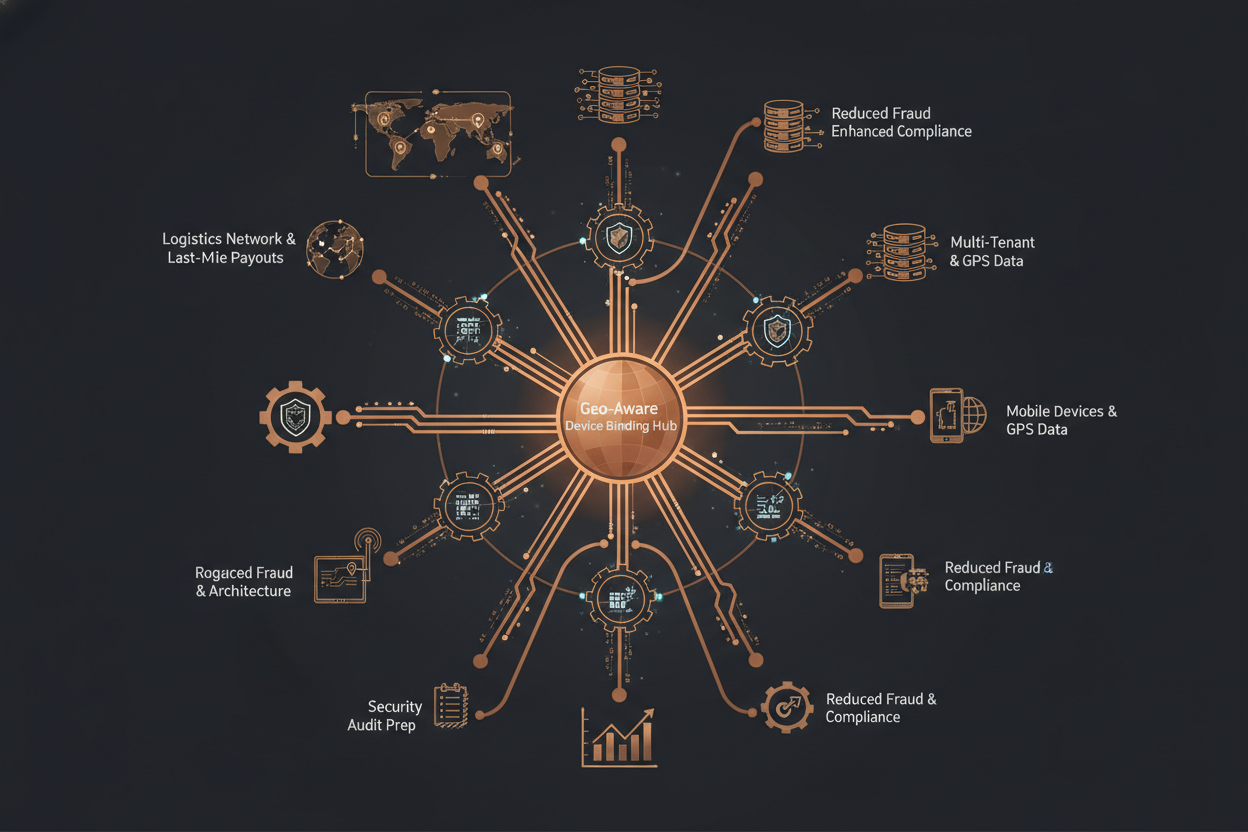
Securing Last-Mile Payouts: A Geo-Aware Device Binding Use Case Spotlight
In the competitive landscape of logistics and last-mile delivery, secure and efficient payout systems are paramount. Fraudsters frequently target these systems, exploiting vulnerabilities to divert funds. A common tactic involves using compromised or spoofed devices to initiate fraudulent payout requests from unexpected geographic locations. Traditional device fingerprinting and IP address checks often fall short against sophisticated attackers who can mask their true location and device characteristics.
Geo-aware device binding offers a robust defense. By linking a device's identity to its expected geographic context, you can create a multi-layered control framework. This goes beyond simple IP-based geolocation. It combines multiple signals, including GPS coordinates captured during normal operations, network triangulation data, and device-specific attributes, to establish a reliable geo-profile for each device. Any transaction originating from a device operating outside its established geo-profile triggers a high-risk alert, prompting further investigation or automated blocking.
Integration Benefits: Stabilizing Fraud Model Performance
- Reduced Fraudulent Payouts: By detecting and blocking transactions from unexpected locations, you directly minimize financial losses due to fraud.
- Improved Fraud Model Accuracy: Geo-aware device data enhances the features available for fraud detection models. This results in higher precision and recall, leading to fewer false positives and more accurate identification of fraudulent activity.
- Enhanced Compliance: Geo-aware device binding assists in complying with regulatory requirements related to KYC (Know Your Customer) and AML (Anti-Money Laundering) by providing a stronger assurance of the legitimacy of transactions.
- Stronger Accountability: Provides better geo decision explainability for regulatory compliance.
Key Risk Indicators: Identifying Geo-Location Discrepancies in Payout Transactions
Successful implementation of geo-aware device binding starts with identifying key risk indicators that highlight potential geo-location fraud. This involves analyzing historical transaction data and establishing baselines for expected device behavior. Here's a checklist of crucial risk indicators to monitor:
Risk Indicator Checklist: Early Detection of Geo-Related Fraud
- Sudden Location Changes: A device abruptly moves from its usual operating location to a significantly different one within a short timeframe.
- Location Inconsistencies: Conflicting location data from multiple sources (e.g., GPS, network triangulation, IP address geolocation) for the same device.
- Unusual Geo-Patterns: Transaction patterns deviate from established norms, such as a device suddenly processing payouts in a new geographic region where it has no prior history.
- High-Risk Geographies: Transactions originating from countries or regions known for high fraud rates or regulatory concerns.
- Velocity Anomalies: A device attempts an unusually high number of payout transactions from a new or unfamiliar location within a short period.
- Proxy Detection: The detection of proxy servers or VPNs, suggesting attempts to mask the device's true location.
- Device Binding Failures: Repeated failures to establish or maintain a valid geo-binding for a device, indicating potential tampering or spoofing.
Anti-Pattern: Relying solely on IP address geolocation for determining device location. Attackers commonly use VPNs and proxies to mask their IP addresses, rendering this method unreliable on its own.
Data Flow and Architecture: Geo-Contextual Device Authorization
Implementing geo-aware device binding requires a well-defined data flow and robust architecture. The system needs to collect, process, and analyze geo-location signals from multiple sources to create a trusted geo-profile for each device. This section outlines the typical data flow and key components involved.
Simplified Data Flow: Securing Payout Requests with Geo-Awareness
- Transaction Initiation: A payout request is initiated from a device. This request includes device identifiers, location data (GPS coordinates if available), and transaction details.
- Data Collection: The system collects additional geo-location signals, such as network triangulation data and IP address geolocation.
- Geo-Profile Lookup: The devices identifiers are used to lookup the existing geo-profile for that device.
- Geo-Contextual Analysis: The collected geo-location data are compared against the device's established geo-profile. Discrepancies are flagged.
- Risk Scoring: A risk score is calculated based on the severity of the geo-location discrepancies and other risk factors.
- Authorization Decision: Based on the risk score, the system makes an authorization decision. High-risk transactions may be blocked, flagged for manual review, or subject to additional authentication steps.
- Audit Logging: All geo-location data, risk scores, and authorization decisions are logged for audit and compliance purposes.
Deployment Steps: Building a Geo-Aware Device Binding System
Implementing geo-aware device binding involves several key steps, from initial setup and configuration to ongoing monitoring and maintenance. Here's a detailed checklist to guide your deployment efforts. This example features a multi-tenant payout system fraud engine where diverse stakeholder policies need consideration.
Implementation Checklist: Integrating Geo-Awareness into Your Security Framework
- Data Source Integration: Integrate data sources like GPS, WiFi triangulation, cellular tower data, and IP geolocation services.
- Device Fingerprinting: Implement robust device fingerprinting to accurately identify and track devices across sessions. Consider using a combination of hardware and software attributes for enhanced accuracy.
- Geo-Profile Creation: Develop a mechanism for creating and maintaining geo-profiles for each device. This should include storing historical location data, identifying frequently visited locations, and establishing acceptable geographic boundaries.
- Risk Scoring Engine: Develop a risk scoring engine that evaluates geo-location discrepancies and assigns a risk score to each transaction. Consider factors such as the severity of the discrepancy, the device's historical behavior, and the transaction amount.
- Policy Configuration: Define policies for handling high-risk transactions. This includes options for blocking transactions, flagging them for manual review, or requiring additional authentication. The policy must consider the preferences of various stakeholders using this fraud engine in a multi-tenant architecture.
- Continuous Monitoring: Implement continuous monitoring of geo-location data and risk scores. Establish alerts for suspicious activity and investigate potential fraud cases promptly.
- Feedback Loops: Create feedback loops to continuously improve the accuracy of geo-profiles and the effectiveness of the risk scoring engine. Incorporate learnings from past fraud cases to refine your detection strategies.
- Integration contract matrix: Establish the contract details for all stakeholders using the fraud engine, including acceptable location accuracy levels, error reporting details, and policy update cadences.
Observability: Monitoring and Fine-Tuning Your Geo-Aware Security
Effective observability is crucial for ensuring the ongoing effectiveness of a geo-aware device binding system. By closely monitoring key metrics and logs, you can identify potential issues, fine-tune your detection strategies, and demonstrate compliance with regulatory requirements.
Observability Checklist: Metrics for Continuous Improvement
- Geo-Profile Accuracy: Track the accuracy of geo-profiles by comparing predicted locations with actual locations. Monitor the rate of false positives and false negatives.
- Risk Score Distribution: Analyze the distribution of risk scores to identify potential biases or anomalies. Ensure that high-risk transactions are being accurately identified.
- Alert Volume: Monitor the volume of alerts generated by the system. Investigate any sudden spikes in alert volume, as this could indicate a potential attack.
- Resolution Time: Track the time it takes to resolve flagged transactions. Aim to minimize resolution time while maintaining accuracy.
- Policy Enforcement: Monitor the effectiveness of policy enforcement. Track the number of transactions that are blocked, flagged, or subjected to additional authentication.
- Audit Logs: Regularly review audit logs to ensure compliance with regulatory requirements. Verify that all geo-location data, risk scores, and authorization decisions are being properly logged.
By implementing these observability strategies, you can gain valuable insights into the performance of your geo-aware device binding system and continuously improve its effectiveness in preventing fraud.
Looking to further refine your fraud detection capabilities? Explore our article showcasing AI-Powered Fraud Detection Examples for Gaming Platforms to learn how machine learning can enhance your geo-aware strategies.
For a deeper dive, see Distributed Rate Limiting: Securing APIs Against Abuse to complement device fingerprinting.
You should also consider Security Through Obscurity vs. Defense in Depth when designing your geo-aware solutions.
Try It In Your Product
Ready to apply this pattern? Start with a free API test, issue your key, and proceed to docs.
Advanced Geo-Fencing Strategies for Complex Logistics
Beyond basic radius-based geo-fencing, sophisticated logistics operations often require more granular control. Consider implementing polygon-based geo-fences for irregular areas or integrating time-based constraints (e.g., deliveries only authorized within specific hours at a location).
Implementing Dynamic Geo-Fences
Dynamic geo-fences adjust automatically based on real-time conditions. For example, a delivery zone might expand during peak hours to accommodate increased traffic or shrink during off-peak hours. Similarly, temporary geo-fences can be created for specific events, such as promotional campaigns or route deviations.
- Define Triggering Events: Identify events that should trigger a geo-fence change (e.g., traffic density exceeding a threshold, scheduled promotional period).
- Automate Geo-Fence Adjustments: Implement a system that automatically adjusts geo-fence boundaries based on the triggering events. This could involve using APIs to update geo-fence configurations in real-time.
- Test Adjustments: Simulate all possible scenarios to improve the accuracy of the rules.
- Monitor Real-Time Performance: Continuously monitor the effectiveness of dynamic geo-fences and make adjustments as needed.
Integrating with Route Optimization Systems
Integrating geo-aware device binding with route optimization systems can enhance both security and efficiency. The route optimization system can use geo-location data to ensure that drivers are following the planned route and to detect unauthorized deviations. You can also use geo-fencing to restrict deliveries to specific areas or to optimize routes based on real-time traffic conditions.
Anti-Patterns in Geo-Fencing
- Anti-Pattern: Overly restrictive geo-fences. Creating geo-fences that are too small or too strict can lead to false positives and disrupt legitimate deliveries. Ensure that your geo-fences are appropriately sized and configured to account for normal variations in location data.
- Anti-Pattern: Neglecting Edge Cases. Failing to consider edge cases, such as situations where a driver needs to briefly exit the geo-fence for a legitimate reason (e.g., restroom break) can cause alerts. Implement a mechanism for handling such edge cases, such as allowing drivers to temporarily disable geo-fencing or providing a grace period for minor deviations.
Strengthening Device Fingerprinting for Enhanced Security
Device fingerprinting plays a crucial role in geo-aware device binding by providing a unique identifier for each device. However, basic device fingerprinting techniques can be easily bypassed by attackers. To enhance security, consider implementing more advanced device fingerprinting methods.
Advanced Device Fingerprinting Techniques
- Canvas Fingerprinting: This technique leverages the unique way in which different browsers render HTML5 canvas elements. While controversial due to privacy concerns, it can provide a highly accurate device fingerprint.
- WebRTC Leak Prevention: WebRTC can leak a device's real IP address, even when using a VPN. Implement measures to prevent WebRTC leaks, such as disabling WebRTC or masking the IP address.
- Behavioral Biometrics: Analyze user behavior patterns, such as typing speed, mouse movements, and scrolling behavior, to create a behavioral fingerprint. This can be used to detect anomalies and identify potentially fraudulent activity.
Checklist: Enhancing Device Fingerprinting Security
- Implement Multi-Factor Fingerprinting: Use a combination of hardware, software, and behavioral attributes to create a more robust device fingerprint.
- Regularly Update Fingerprinting Scripts: Keep your fingerprinting scripts up-to-date to detect and prevent evasion techniques.
- Monitor Fingerprint Stability: Track the stability of device fingerprints over time. A sudden change in fingerprint can be an indicator of device spoofing.
- Obtain Consent: Explicitly inform users about device fingerprinting and obtain their consent before collecting data.
Responding to Geo-Location Spoofing
Even with robust geo-aware device binding, attackers may still attempt to spoof their location. Implement mechanisms for detecting and responding to such attempts.
Real-time Spoofing Detection
Implement real-time spoofing detection mechanisms to identify suspicious location data. These checks can trigger alerts or require additional authentication.
- Velocity Checks: Monitor the speed at which the device is moving. If the device is moving faster than is physically possible, it may be an indication of location spoofing.
- Sudden Jumps: Detect sudden and unexplained jumps in location. These jumps can indicate that the device's location is being artificially manipulated.
- Inconsistent Signals: Compare location data from multiple sources (e.g., GPS, WiFi, cellular). Inconsistencies between these signals can indicate spoofing.
Scaling Geo-Aware Systems for High Transaction Volumes
Geo-aware device binding can be computationally intensive, especially at high transaction volumes. Optimize your system for scalability to ensure that it can handle a large number of requests without impacting performance.
Scalability Strategies
- Asynchronous Processing: Processing location data and risk scores asynchronously can significantly improve performance. Offload these tasks to a message queue or background processing system.
- Caching: Cache frequently accessed geo-profiles and risk scores to reduce database load.
- Horizontal Scaling: Distribute the workload across multiple servers to increase capacity.
- Database Optimization: Optimize your database queries and indexes to improve performance. Consider using a database specifically designed for geo-spatial data.
Example Implementation: Geo-Fence Validation in Golang
This code snippet demonstrates a simplified approach to checking if a GPS coordinate is within a geo-fence. This example uses the `github.com/paulmach/go.geo` library.
```go package main import ( "fmt" "github.com/paulmach/go.geo" ) func main() { // Define the geo-fence polygon polygon := geo.NewPolygon([]geo.Point{{ {-74.0060, 40.7128}, // New York City {-118.2437, 34.0522}, // Los Angeles {-87.6298, 41.8781}, // Chicago }}) // GPS coordinate to check latitude := 40.7128 longitude := -74.0060 point := geo.NewPoint(longitude, latitude) isWithin := polygon.Contains(point) fmt.Printf("The point (%f, %f) is within the polygon: %t\n", latitude, longitude, isWithin) } ```Next step
Run a quick API test, issue your key, and integrate from docs.