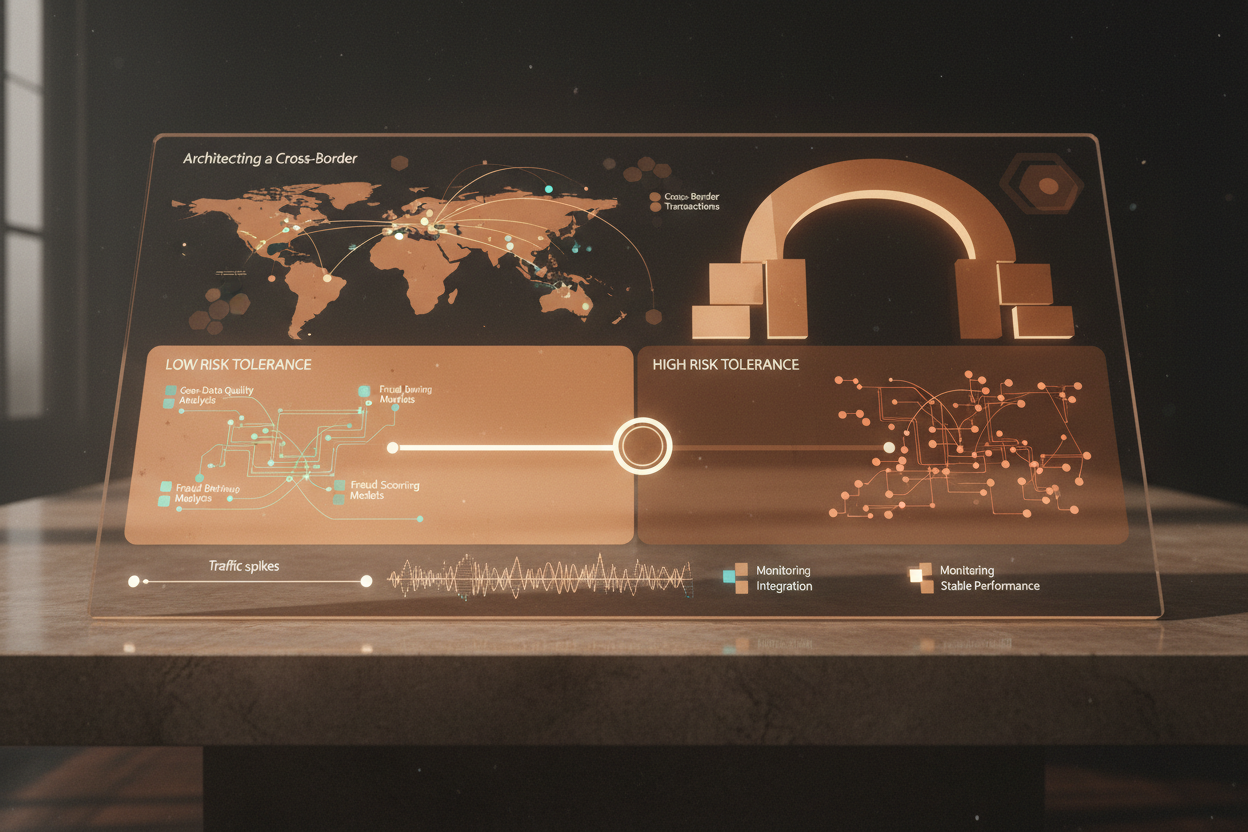
Architecting a Cross-Border fraud exposure index for logistics payout integrity
The Problem: Payout Fraud in Cross-Border Logistics and the Need for a CBFEI
Global logistics networks face increasing threats from payout fraud, particularly in cross-border transactions. The complexity of international operations, involving multiple currencies, regulatory frameworks, and payment systems, provides ample opportunity for fraudulent activities. These can range from simple billing discrepancies to sophisticated schemes involving identity theft and synthetic fraud.
A reactive approach to fraud detection is insufficient. We need proactive measures capable of identifying and mitigating vulnerabilities before losses occur. The Cross-Border Fraud Exposure Index (CBFEI) offers a structured, data-driven approach to assess and manage fraud risk in cross-border logistics payouts. By systematically analyzing various risk factors and integrating them into a comprehensive scoring model, the CBFEI enables organizations to prioritize resources, implement targeted controls, and reduce overall fraud exposure.
Defining Data Inputs for a Cross-Border Fraud Exposure Index
The foundation of a robust CBFEI lies in the quality and relevance of its data inputs. A comprehensive assessment requires gathering data from diverse sources and ensuring its integrity. Here's a breakdown of critical data categories:
Transactional Data
- Payout Amount and Currency: Track the amounts and currencies involved in each transaction. Anomalies in payout size or unusual currency conversions can be indicative of fraudulent activity.
- Payment Method: Scrutinize payment methods used for payouts. Certain methods may be more vulnerable to fraud in specific regions.
- Transaction Timestamp: Analyze the timing of transactions. Unusual patterns, such as transactions initiated outside of normal business hours or on holidays, can raise suspicion.
- Recipient Account Details: Collect information about the recipient's bank account, including the account number, bank name, and country. Validate these details against other available data sources.
Geographic Data
- Origin and Destination Countries: Identify the countries involved in the transaction. Some countries may have higher fraud rates or weaker regulatory oversight.
- IP Address and Geolocation: Capture the IP address of the device used to initiate the transaction and determine its geographic location. Discrepancies between the IP address location and the recipient's address can be a red flag. The quality of GeoIP data plays a crucial role at this step.
- Distance and Routing: Calculate the distance between origin and destination points and analyze the routing path. Unusual deviations or illogical routes may indicate fraud.
User and Entity Data
- User Identification: Require users to provide identification information, such as their name, address, and date of birth. Verify this information against external databases.
- Device Fingerprinting: Collect data about the user's device, including the operating system, browser version, and installed plugins. Use this information to create a unique fingerprint for each device and detect instances of device spoofing.
- Entity Verification: For business payouts, verify the legitimacy of the recipient entity. Check its registration status, ownership details, and financial history.
Geo Data Quality Audit Checklist
To ensure the reliability of geographic data, conduct regular audits using the following checklist:
- Accuracy Verification: Compare geolocation data from multiple sources to identify discrepancies and inaccuracies.
- Data Completeness: Check for missing or incomplete geographic data fields.
- Consistency Checks: Ensure consistency between different geographic data fields, such as country codes and regional designations.
- Recency Validation: Verify that geographic data is up-to-date and reflects the latest changes in addresses, boundaries, and postal codes.
- Coverage Assessment: Assess the coverage of geographic data across different regions and countries. Identify areas where data coverage is limited or unreliable.
Signal Analysis: Identifying Fraud Indicators in Cross-Border Transactions
Once the data inputs are collected, the next step is to analyze them for potential fraud indicators. Signal analysis involves applying statistical and machine learning techniques to identify patterns and anomalies that suggest fraudulent activity.
Statistical Analysis
- Outlier Detection: Identify transactions with payout amounts or frequencies that deviate significantly from the norm.
- Correlation Analysis: Examine the relationships between different data variables. For example, a strong correlation between high payout amounts and specific geographic regions may indicate a fraud hotspot.
- Time Series Analysis: Analyze transaction data over time to detect seasonal patterns or sudden spikes in fraudulent activity.
Machine Learning Techniques
- Anomaly Detection: Employ machine learning algorithms to detect unusual patterns or deviations from expected behavior.
- Classification Models: Train machine learning models to classify transactions as either fraudulent or legitimate based on their features.
- Clustering Analysis: Group similar transactions together based on their characteristics. This can help identify fraud rings or organized fraud schemes.
Examples of Fraud Indicators
- IP Address Mismatch: The IP address of the device used to initiate the transaction does not match the recipient's location.
- Unusual Transaction Timing: The transaction is initiated outside of normal business hours or on a holiday.
- High-Risk Country: The transaction involves a country with a high fraud rate or weak regulatory oversight.
- Multiple Accounts from Same Device: Several accounts are accessed from the same device, potentially indicating account takeover.
- Rapid Payout Requests: A recipient requests multiple payouts in a short period of time.
Developing a Robust Risk Scoring Model
The risk scoring model aggregates the signals identified in the previous step into a single score that represents the likelihood of fraud. This score allows organizations to prioritize transactions for further review and implement appropriate mitigation measures.
Components of a Risk Scoring Model
- Feature Selection: Identify the most relevant fraud indicators to include in the model.
- Weighting: Assign weights to each feature based on its predictive power and importance.
- Scoring Scale: Define a scoring scale that ranges from low to high risk.
- Thresholds: Establish thresholds for different risk levels, triggering specific actions (e.g., manual review, suspension of payout).
Building the Model
- Data Preparation: Clean and preprocess the data to ensure it is suitable for model training.
- Model Training: Train a machine learning model using historical transaction data labeled as fraudulent or legitimate.
- Model Validation: Validate the model's performance on a separate dataset to ensure its accuracy and generalizability.
- Model Calibration: Calibrate the model to ensure that the scores accurately reflect the probability of fraud.
Anti-Patterns in Risk Scoring Model Development
- Overfitting: The model performs well on the training data but poorly on new data.
- Data Leakage: Including information in the model that is not available at the time of prediction.
- Bias: The model is biased towards certain demographics or geographic regions.
Integrating the CBFEI into Payout Systems
Integrating the CBFEI into existing payout systems requires careful planning and execution. The goal is to seamlessly incorporate fraud detection capabilities into the payout process without disrupting normal operations.
Integration Steps
- API Integration: Integrate the CBFEI into the payout system using APIs. This allows for real-time risk scoring of transactions.
- Data Enrichment: Enrich transaction data with additional information from external sources, such as fraud databases and credit bureaus.
- Workflow Automation: Automate the review process for high-risk transactions. This may involve routing transactions to fraud analysts for further investigation.
- Alerting and Reporting: Configure alerts to notify relevant personnel of suspicious activity. Generate reports to track fraud trends and model performance.
Practical Example: Zero-Trust Access Review Triggered by Anomalous Admin Sessions
Suppose an administrator in a logistics company initiates a series of cross-border payout adjustments after logging in from an unusual IP address outside their typical location. The CBFEI would flag this session as high-risk due to the IP address mismatch and the sensitive nature of the transactions. A zero-trust access review would then be triggered, requiring the administrator to re-authenticate using multi-factor authentication and provide justification for the adjustments. This proactive approach prevents potential fraud by verifying the administrator's identity and intent before the payouts are processed. This illustrates how to apply real-time data enrichment.
Developing a Comprehensive Monitoring Plan
Continuous monitoring is essential to ensure the effectiveness of the CBFEI and to adapt to evolving fraud trends. A robust monitoring plan should include the following components:
Key Performance Indicators (KPIs)
- Fraud Rate: The percentage of transactions that are identified as fraudulent.
- False Positive Rate: The percentage of legitimate transactions that are incorrectly flagged as fraudulent.
- Detection Rate: The percentage of fraudulent transactions that are successfully detected.
- Review Time: The time it takes to review and resolve flagged transactions.
- Cost of Fraud: The total financial losses resulting from fraudulent transactions.
Monitoring Activities
- Real-time Monitoring: Continuously monitor transaction data for suspicious activity.
- Model Performance Monitoring: Track the performance of the risk scoring model and identify areas for improvement.
- Fraud Trend Analysis: Analyze fraud trends to identify emerging threats and vulnerabilities.
- Regular Audits: Conduct regular audits of the CBFEI to ensure its accuracy and effectiveness.
Addressing Billing Edge Cases Across Regions
Cross-border operations often involve complex billing scenarios that can create edge cases for fraud detection. For example, variations in VAT rates, currency exchange fees, and local taxes can make it difficult to identify fraudulent transactions based solely on payout amounts. To address these edge cases, it is essential to incorporate regional billing rules and regulations into the CBFEI. This may involve creating separate risk scoring models for different regions or implementing dynamic thresholds that adjust based on local billing practices.
Wrap-Up: CBFEI as a Foundation for Logistics Payout Integrity
The Cross-Border Fraud Exposure Index provides a structured, data-driven approach to mitigating payout fraud in global logistics operations. By carefully selecting data inputs, applying signal analysis techniques, building a robust risk scoring model, integrating the model into payout systems, and implementing a comprehensive monitoring plan, organizations can significantly reduce their fraud exposure and protect their financial interests. Furthermore, the CBFEI supports zero-trust principles and can trigger enhanced authentication during potentially compromised sessions, safeguarding payouts at scale.
Consider exploring Advanced Threat Detection in Fintech to discover more ways to enhance your systems.
Try It In Your Product
Ready to apply this pattern? Start with a free API test, issue your key, and proceed to docs.
Next step
Run a quick API test, issue your key, and integrate from docs.