Examples & Guides
Practical implementation patterns, antifraud playbooks, and production-ready integration recipes.
Use this section as a working library: architecture ideas, rollout checklists, and clear examples
for login, signup, checkout, and anti-abuse scenarios.

Learn how to combine geolocation data with device fingerprinting for stronger fraud prevention in fintech systems. This article explores practical implementation techniques to enhance security and reduce risk. Includes code examples and architecture design considerations.
Read article

Implement robust risk scoring for roaming mobile IP addresses in fintech to mitigate fraud and ensure compliance. This article details a practical approach to manage the unique challenges of mobile roaming in financial transactions.
Read article
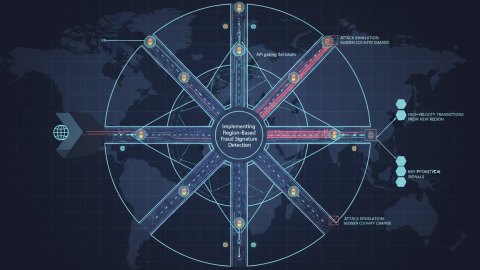
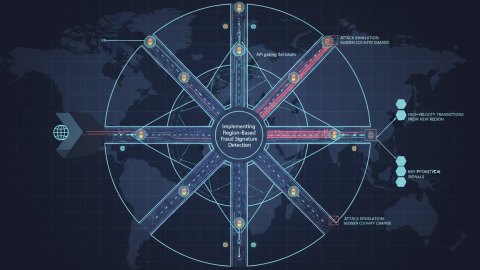
This field report details the practical implementation of region-based fraud signature detection, focusing on architectural decisions, implementation specifics, and lessons learned. We explore attack simulations, key detection signals, and effective countermeasures, emphasizing a hands-on approach.
Read article

Explore the architecture of location-based fraud detection experimentation. Learn how to model location data, engineer effective features, and deploy robust scoring models for real-time risk assessment, including examples.
Read article

This playbook details how to implement robust validation for cross-border merchant onboarding using GeoIP data, mitigating risks associated with fraudulent or non-compliant businesses. Learn practical steps, detection logic, and validation strategies.
Read article

This guide provides a technical deep-dive into tracking the lifecycle of geo anomalies using IP geolocation data. We'll cover detection, investigation, and resolution strategies with practical code examples for streamlined implementation, maximizing the effectiveness of your antifraud systems. Streamline your antifraud efforts; sign up today!
Read article
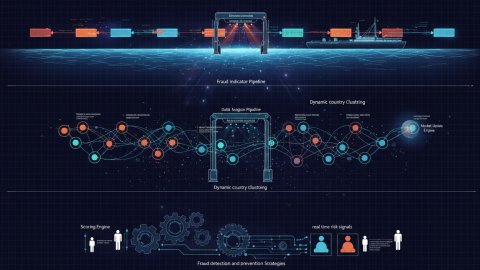
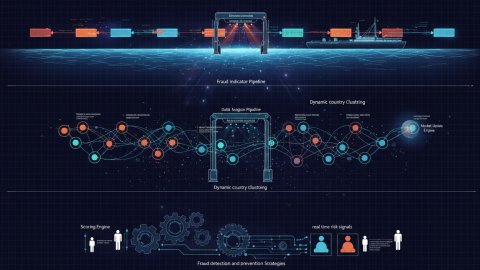
Explore dynamic country clustering for fraud modeling. Learn how to group countries based on real-time fraud patterns, enhancing your fraud detection and prevention strategies.
Read article

Learn how to build a digital trust architecture using GeoIP data to defend against sophisticated payment fraud rings. This guide walks through a real incident breakdown, detection methods, geo trace reconstruction, and long-term control implementation.
Read article

This article provides a technical review framework for designing and implementing location-aware fraud KPI models using GeoIP data. It covers data sourcing, methodology, relevant metrics, and practical implementation details to enhance fraud detection and prevention strategies. It concludes with a discussion about model performance and ongoing evaluations.
Read article

Implementing a robust geo anomaly detection system requires careful weighting of various signals. This guide provides a practical, API-focused approach to building a framework that prioritizes accuracy and reduces false positives, improving your fraud prevention efforts. Learn how to leverage GeoIP.space API for optimal signal weighting.
Read article